In the digital world, online identities and activity locations can be easily traced through domains and hosting.
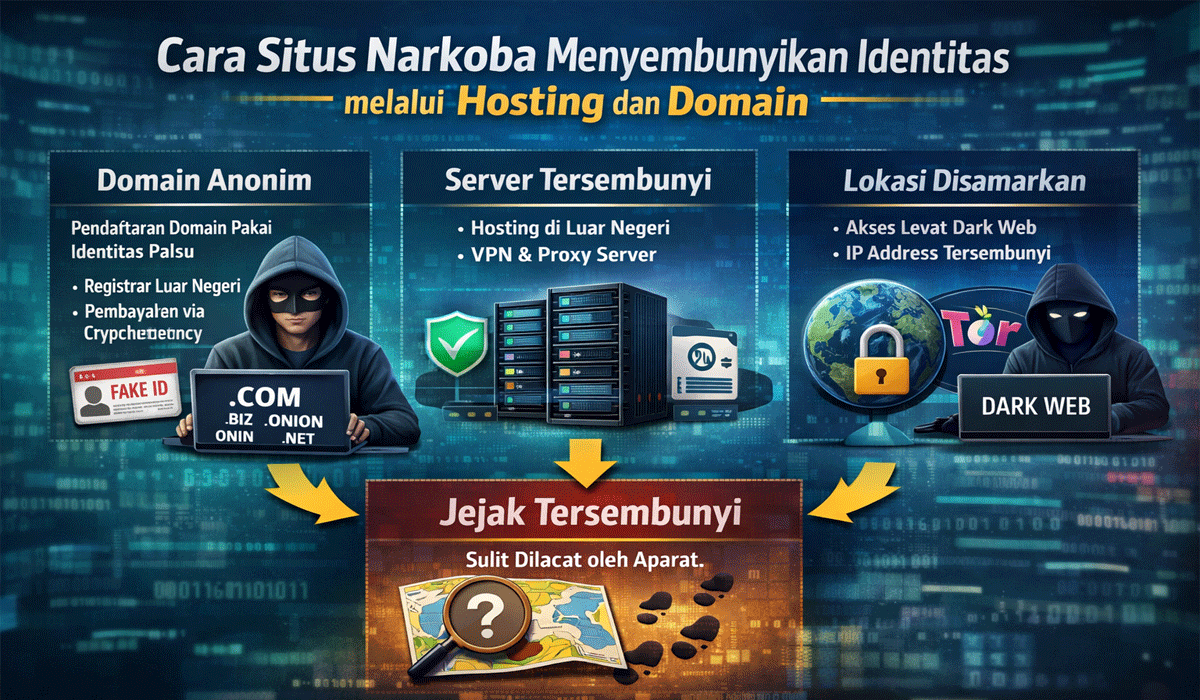
However, drug networks have developed sophisticated methods to conceal their tracks, using internet technology to operate anonymously. By leveraging hard-to-trace domain names and hidden or frequently changing web hosting, they aim to maintain secrecy while conducting illegal operations. Understanding these techniques is crucial for law enforcement, cybersecurity experts, and the public to remain vigilant against dangerous practices in cyberspace.
This article Web Hosting And Domain Names explores in detail the strategies used to obscure digital identities and their implications.
Domain Name Selection Strategies
Domain names serve as the primary identity in the online world. Drug networks typically select names that appear innocuous and are difficult to trace, often using a combination of letters, numbers, or seemingly random words. The goal is to avoid detection by authorities monitoring domain registrations. Domains may also be frequently changed, keeping digital identities fluid and harder to follow.
In addition, some domains are registered through third-party or anonymous services, making the true owner invisible. This creates a buffer between digital activity and real-world identities, complicating investigations. Understanding these domain selection techniques allows authorities to develop strategies to track suspicious digital addresses effectively.
Web Hosting And Location Concealment
Web hosting determines where digital data is physically stored. Drug networks often choose servers located in countries with weak regulations or low transparency, making them difficult to access by law enforcement. Some also use cloud-based or hidden hosting to mask the actual location, making digital activity harder to map.
Additional technologies, such as data encryption and Virtual Private Networks (VPNs), are employed to add layers of protection. Despite these measures, every interaction leaves traces, including IP addresses and access logs. Careful analysis of these logs enables researchers to detect server patterns and locations, revealing concealment strategies.
Encryption And Anonymity Techniques
Encryption is a key method used to hide content and identity. Encrypted data can only be accessed by those with the correct key, preventing third parties from reading sensitive information. Drug networks use encryption for internal communications and the transmission of sensitive data.
Anonymity is further strengthened through fake digital identities and temporary email addresses. This combination makes tracking the real owner challenging and increases the complexity of digital investigations. Understanding these techniques helps security experts develop more effective mitigation and prevention strategies.
Read Also: The Secret To Choosing a Domain Name That’s Easy To Remember And Attracts Customers
Activity Patterns And Digital Footprint Analysis
Even when identities are hidden, digital activity leaves footprints. Every interaction with a domain and server generates data that can be analyzed, including access times, user locations, and communication patterns. Using big data and network analysis, authorities can connect seemingly isolated points into identifiable patterns.
Pattern analysis not only aids investigations but also enables early detection of suspicious activity. Identifying new domain registrations, specific server usage, and digital content distribution can serve as early warning indicators. Understanding digital footprints strengthens preventive measures before illegal operations spread widely.
The Role of Regulations And Public Awareness
Internet regulations are critical in limiting the misuse of domains and hosting. Each country has different rules regarding domain ownership, data storage, and service providers’ obligations to report suspicious activity. International cooperation is necessary because digital activity often crosses national borders.
Public awareness also plays an important role in prevention. Education about digital security, including strong passwords, two-factor authentication, and monitoring online activity, helps individuals protect themselves. Public participation in recognizing and reporting suspicious activity acts as the first line of defense against the spread of drug operations online.
Conclusion
Drug networks use a combination of domains, hosting, encryption, and anonymity to hide their identities online. While these strategies complicate tracing and investigations, careful analysis of digital patterns can reveal their activities.
Prevention requires a collaborative approach involving regulations, technology, and public awareness. By understanding digital concealment techniques, individuals can protect themselves and contribute to a safer online environment. Together, these measures are key to creating a more secure internet for everyone.